Healthcare Security and PHI Protection Built for Real-World Compliance
We design and operate healthcare platforms that handle PHI under executed Business Associate Agreements, continuous HIPAA compliance monitoring, and production-grade security controls. Our systems manage ePHI across 130+ clinical locations today.
Digital Scientists is a HIPAA-compliant software development partner for health systems, payers, and digital health companies. We deliver ePHI safeguards, secure SDLC practices, and healthcare platform security from concept through production operations.
- HIPAA Administrative, Technical, and Physical safeguards mapped to the Security Rule
- Executed BAAs and downstream subcontractor coverage for every engagement
- Secure SDLC with automated testing, code review, and penetration testing
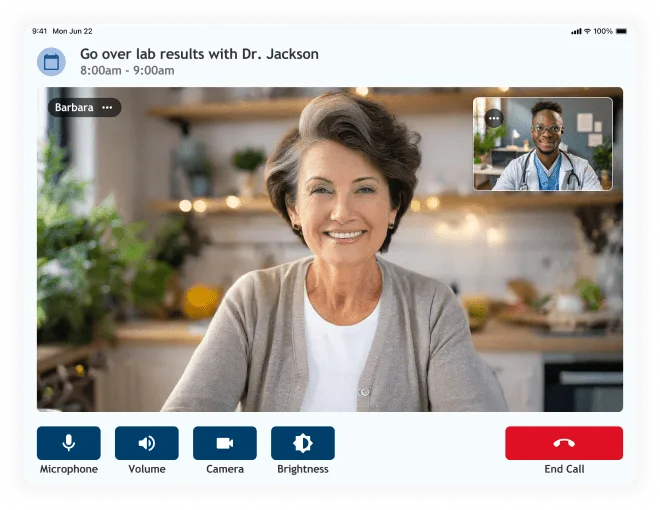
Compliance in Production with NeverAlone — 100K+ calls/yr
Where we stand today
Transparency is the starting point. Here is our current compliance status, what we have achieved, and what we are working toward.
HIPAA Compliance
We operate as a HIPAA-compliant business associate. Our security controls, workforce training, and data handling practices meet the HIPAA Security Rule, Privacy Rule, and Breach Notification Rule. We execute a BAA with every covered entity and subcontractor — no exceptions.
SOC 2 Type II
We are working toward SOC 2 Type II. We are not yet certified. Our controls and evidence collection run on ERAMBA.
HITRUST CSF
HITRUST r2 certification is on our roadmap. We do not hold HITRUST certification today.
Continuous Compliance Governance: Our compliance program runs on ERAMBA, an enterprise GRC platform. This gives us centralized policy management, automated control assessments, risk registers, and real-time compliance dashboards — continuous, evidence-based assurance that our controls are working.
Our BAA process
Every engagement that involves PHI starts with an executed BAA. Here is how we handle it.
Scope Review
We assess whether the engagement involves PHI or ePHI. If it does — or could — we initiate a BAA before any data is exchanged or system access is granted.
Agreement Execution
We work with your legal and compliance teams to execute a BAA that defines permitted uses, disclosure limitations, safeguard obligations, and breach notification requirements.
Subcontractor Chain
We maintain BAAs with our own vendors and subcontractors who may access PHI, covering the entire chain of custody — including cloud infrastructure providers like AWS and Azure.
Ongoing Obligations
BAAs are not filed and forgotten. We conduct periodic reviews and maintain documentation of our compliance posture throughout the engagement — and after data return or destruction.
People, policies, and governance
Technical controls are only as strong as the people and processes behind them. Our administrative safeguards address workforce security, risk management, and incident readiness.
Security Risk Analysis
We conduct periodic security risk analyses to identify threats to ePHI. Findings feed into our ERAMBA risk register, where each risk is scored, assigned an owner, and tracked through mitigation. Risk assessments are repeated annually and after significant system changes.
Workforce Training
All team members complete HIPAA Security and Privacy awareness training at onboarding and annually thereafter. Training covers PHI handling, breach identification, social engineering, and reporting obligations.
Security Policies & Governance
Our information security policies are documented, version-controlled, reviewed annually, and managed through ERAMBA. All team members acknowledge policies and updates in writing. Governance includes defined roles, accountability, and regular compliance reviews.
Incident Response
We maintain a documented incident response plan that meets HIPAA Breach Notification Rule requirements. Real-time monitoring identifies potential incidents. Critical incidents are escalated within one hour. If a breach of PHI is confirmed, we notify affected covered entities within BAA-specified timeframes — well within the HIPAA 60-day window. Every incident concludes with a blameless post-mortem and tracked remediation actions.
Background Screening
We conduct background screening for all personnel who will have access to PHI or client systems, consistent with the sensitivity of the data and access level involved.
Onboarding & Offboarding
New team members complete security training and policy acknowledgment before receiving any system access. When team members leave an engagement or the company, access is revoked within 24 hours. Documented checklists cover device return, credential revocation, and access audit verification.
Track record: Digital Scientists has not experienced a breach of protected health information.
Proven in production: These are not theoretical controls. We maintain incident readiness for NeverAlone, our EHR-integrated clinical platform used 24/7 across 130 locations — where uptime, data integrity, and security directly impact patient care.
Security built into every layer
From encryption and access control to automated testing and continuous monitoring, our technical safeguards protect ePHI throughout its lifecycle.
Encryption
All ePHI is encrypted at rest using AES-256 and in transit using TLS 1.2 or higher. Encryption keys are managed through cloud-native key management services (AWS KMS, Azure Key Vault) with automatic rotation and access-logged key usage.
Access Control
We enforce role-based access control (RBAC) with the principle of least privilege. Access to PHI requires multi-factor authentication (MFA). All access is logged, and we conduct quarterly access reviews to verify entitlements match current roles.
Audit Logging
Immutable audit trails capture all access to PHI — who accessed what, when, and from where. Logs are centrally aggregated and retained according to HIPAA-compliant retention policies.
Data Minimization
We collect and process only the minimum PHI necessary for the engagement. Development and testing use de-identified or synthetic data sets. Production PHI access is reserved for validated environments only.
Secure SDLC
Security requirements are defined during discovery and validated at every stage: design reviews, threat modeling, code reviews, automated testing, and pre-deployment security gates.
Automated Security Testing
SAST and DAST run in CI/CD pipelines. Dependency scanning flags known vulnerabilities in third-party libraries before they reach production.
Code Review & Pen Testing
All code changes are peer-reviewed with security-specific criteria. No code merges to production without an approved review. We conduct regular penetration testing using both internal assessments and third-party firms.
Intrusion Detection & SIEM
We deploy network and host-based IDS, SIEM for centralized log analysis, and real-time alerting. Anomalous access patterns trigger automated investigation workflows.
Vulnerability Management
Continuous vulnerability scanning of infrastructure and application layers. Critical findings are triaged within 24 hours and patched according to severity-based SLAs.
Cloud-native, healthcare-hardened
We build on HIPAA-eligible cloud services with BAAs in place at the infrastructure level.
Network Isolation
PHI workloads run in dedicated VPCs with private subnets, network ACLs, and security groups that restrict traffic to explicitly authorized paths. No public internet exposure for data stores.
Infrastructure as Code
All infrastructure is provisioned through Terraform and/or AWS CloudFormation, delivering consistent, repeatable, and auditable configurations. No manual infrastructure changes in production.
Backup & Disaster Recovery
Automated encrypted backups with point-in-time recovery. Backup integrity is tested regularly, and recovery procedures are documented and rehearsed with defined RTOs and RPOs.
Cloud Provider BAAs
We maintain executed BAAs with our cloud infrastructure providers. All PHI workloads are deployed exclusively on HIPAA-eligible services within U.S. regions.


Hybrid delivery under controlled access
Our delivery model separates security oversight from development execution, with consistent controls applied across all team members regardless of location.
US-Based Security Oversight
Security architecture and compliance decisions are led by our US-based team. This includes risk analysis, BAA execution, incident response, and all communication with your security and compliance stakeholders.
Controlled Production Access
All production access requires VPN, managed devices, and MFA. Every access event is logged and monitored. No team member accesses production systems from personal devices.
Role Separation
Development, test, and production access is separated by role. PHI access is granted per engagement and per individual. Developers working on non-PHI components do not touch production data.
Managed Nearshore Under Controls
Nearshore team members operate under the same security policies, HIPAA training, background screening, and access controls as US staff. No exceptions.
We make your security review easy
We know what procurement and security teams need. Here is what we provide to move your evaluation forward.
Security Questionnaires
We complete SIG, CAIQ, HECVAT, and custom security questionnaires. Our responses are pre-filled and updated quarterly so turnaround is fast.
Architecture Diagrams
We provide network architecture, data flow, and system boundary documentation. Diagrams are engagement-specific and updated as systems change.
Data Flow Documentation
PHI ingress, storage, access, processing, and disposal are documented per engagement. We map every touchpoint where ePHI is handled.
BAA Templates
We provide a standard BAA template or work from yours. Turnaround is under one week from initiation to execution.
Pen Test Coordination
We coordinate with your penetration testing firm or share results from our most recent third-party assessment. We support scoped testing against staging or production environments.
Direct Technical Access
Your security team talks directly to our technical leadership. No sales intermediary. We answer architecture, compliance, and implementation questions in detail.
How ePHI moves through our systems
Data Ingress
TLS 1.2+ encrypted APIs
Encrypted Storage
AES-256 at rest, cloud-native KMS
Access Controls
RBAC + MFA, least privilege
Monitoring
Audit logs, SIEM, IDS
Encrypted Backups
Automated, tested, point-in-time recovery
Data Ingress
TLS 1.2+ encrypted APIs
Encrypted Storage
AES-256 at rest, cloud-native KMS
Access Controls
RBAC + MFA, least privilege
Monitoring
Audit logs, SIEM, IDS
Encrypted Backups
Automated, tested, point-in-time recovery
Questions from procurement & security teams
Ready to evaluate our security posture?
We will walk you through our compliance documentation, complete your security questionnaire, and execute a BAA so your team can move forward.